|
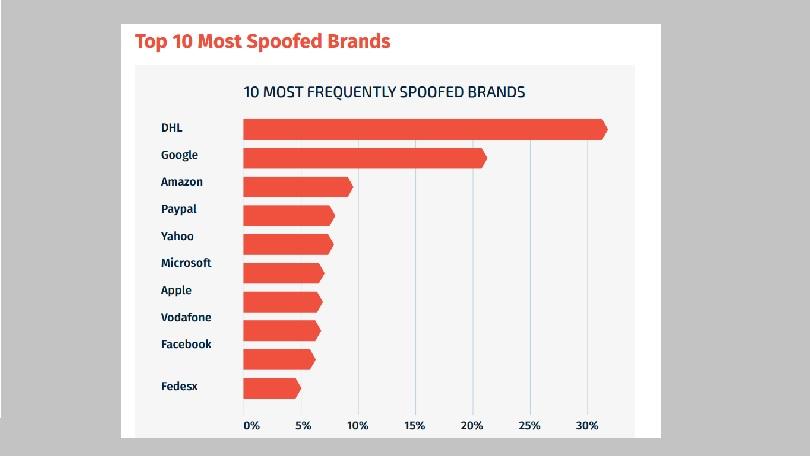
When Democratic National Committee (DNC) Chief John Podesta's aide forwarded him an email that claimed Podesta's Gmail account was hacked, Podesta did what most of us would have done: He clicked the link within the email and was directed to a website where he was prompted to enter a new password. He did so and then went about his daily business. Unfortunately for Podesta, the Democratic Party, and Hillary Clinton's presidential campaign, the email sent to Podesta wasn't from Google. Rather, it was a spear-phish attack from a Russian hacking group named "Fancy Bear." Even if you've never heard of the term "spear-phishing," you've undoubtedly heard of these kinds of attacks. You've probably even been a target of them. These attacks typically take the form of customer support emails that ask you to change credentials or they can be sent via fake email addresses to businesses asking for highly personal customer or employee data. For example, in 2015, employees of Ubiquiti Networks transferred $46.7 million to overseas accounts at the behest of emails the employees assumed were sent by Ubiquiti executives. In reality, hackers created spoof email accounts that bore a resemblance to actual Ubiquiti executive accounts and tricked the employees. Based on data from a recent study conducted by email security company IronScales, 77 percent of attacks are laser-focused, targeting 10 accounts or fewer, with a third of attacks targeting only one account. Attacks are short, with 47 percent lasting less than 24 hours, and 65 percent lasting fewer than 30 days. Traditional spam filters and endpoint protection tools aren't catching the attacks. For every five attacks identified by spam filters, 20 attacks made it into a user's inbox. "We see attackers spending much more time studying their targets than in years past, running a very comprehensive reconnaissance process," said Eyal Benishti, CEO of IronScales. "As a result, phishing emails have become highly targeted and tailored to the target company, as attackers are able to gather information through reconnaissance that helps them craft emails to look like legitimate internal communication. For example, we've seen some attacks use the organizations' lingo and signatures, and the content is very much in context to what is currently running inside the company and between trusted parties." Jeff Pollard, Principal Analyst at Forrester Research, added that these attacks are also growing in sophistication. "Attacks are getting more sophisticated both in terms of the lures used to get people to click and in terms of the malware used to gain entry to systems," said Pollard. "But that is what we expect given that cybersecurity is a constant battle between defenders and attackers." The SolutionTo combat these attacks, companies are turning to anti-phishing software to detect and flag incoming attacks. Anti-spam and anti-malware tools are no-brainers for any company hoping to protect business data. But companies such as IronScales are taking it a step further by layering in machine learning (ML) tools to proactively scan for and flag sketchy phishing emails. Additionally, because ML lets the tools compile or remember scam data, the software learns and improves with every scan. "The technology makes it harder on the attacker to fool the defender with small tweaks that normally bypass a signature-based solution," said Benishti. "With ML, we can quickly cluster different variants of the same attack and more effectively fight against phishing. In fact, from our analysis, ML is the best way to train a system to tell the difference between legitimate emails coming from a trusted partner or colleague versus a non-legitimate one." Technology isn't the only safeguard against these forms of attacks. Education and caution are perhaps the most important defenses against spear-phishing attacks. "Some businesses are aware of the threats, though others mistakenly believe that their current solution is protecting against targeted attacks," said Benishti. "It's very important to understand that using the same defense mechanisms and expecting different results in future attacks simply won't do. Using technology alone against advanced attacks, which put people as targets, will always fail, as will relying solely on employee awareness and training…People and machines working closely together to close this gap of unknown attacks is the only way to reduce risk." How to Stay SafeHere are a few very simple ways to ensure that you and your company don't get scammed:
Unfortunately, no matter how careful you may be, attacks will intensify and become more intelligent. You can do everything in your power to educate yourself and your employees, you can build out an anti-phishing defense backed by new technologies, and you can take every precaution possible. But, as Pollard noted, "it only takes one bad day, one mis-click, or one rushed user trying to clean out an inbox, to lead to catastrophe."
0 Comments
Remember the awe you felt when you turned on your new computer and it loaded in a flash? Your computer was the envy of your friends and you weren’t afraid to bathe in that glory. Button on, ready to go, those were the days!
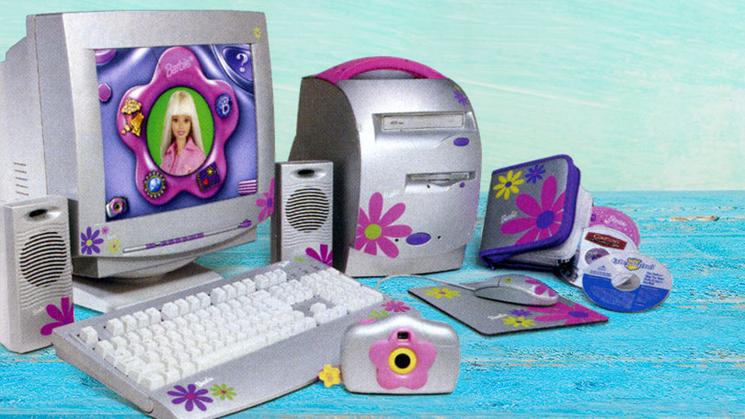
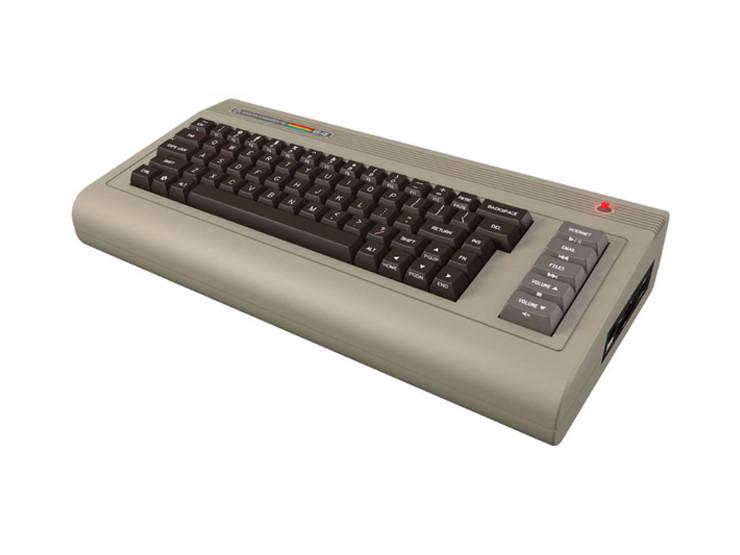
After a year or two though, it doesn’t seem to be quite as zippy…no, you’re not imagining it. It really has slowed down, not just in comparison to newer models and your expectations…There’s a measurable drop in speed and power that has nothing to do with worn out parts. The good news is a little maintenance can have that baby cruising at top speed again. Let’s take a leisurely walk through the system and spot the culprits: Start-up applications: It’s super convenient to have Skype start automatically and your anti-virus too. In fact, many of the applications starting themselves with the computer are essential to your experience. But some of them are getting a little too ‘helpful’. For example, iTunes helper loads in the background to speed things up when you connect your device – but if you can’t even remember the last time you ran iTunes on your computer, then it can go. Programs like that are holding onto a portion of your processing power and adding to your speed issues. The average home computer automatically loads around 75 programs at start-up! Temporary junk: Computers are kind of messy. They leave temporary files and snippets of information all over your hard drive, each action leaving a trail rather like a roaming toddler with a sticky sandwich. Every web page, every image on that web page, every program you run and every game you play leaves something behind. It may be the tidbits of information called “cookies”, saved game files, auto-restore files or even a log so that you can hit the undo button 100 times while it remembers your actions for you. The more junk your computer builds up, the slower it gets. Viruses and malware: These infections sit in the background consuming resources while doing various nightmarish things. They may be spying on your actions, stealing your information or reaching out through your network to infect others. Occasionally, the impact is limited to seeing your computer slow to a crawl, however, the flow-on financial costs of an infection can easily reach into the thousands. Bloating: With every new version of software comes a new set of features, introductory sequences and design improvements. The problem with this is the application becomes larger and larger with each new version, requiring more system resources to install and run – and slowing your computer down. Just like a car, computers need regular maintenance – we offer a Tune-Up service to bring your computer back to its original speed and extend its life. Give me a call at 778-997-2533 to book in a Tune Up. If you've spent any time reading tech news sites, you've no doubt seen galleries of weird and wild PC modifications—usually called "case mods"—done by individuals on a one-time basis. Those are fun, sure, but what's more amazing to me is that giant corporations have created their very own "case mods" on a mass-produced or commercial scale. They involve strange and unusual designs that might have very well been mistaken as the creations of a clever computer fanatic. Bravely, those firms were willing to take a chance on a crazy design idea. Sometimes those risks worked out for the best, and some times they failed miserably. In the gallery below, you'll see 10 bizarre PC designs of late (the past 17 years, as it happens). Most of them failed, but we can't help but admire the companies for trying. Barbie PC (2000)Unsatisfied with Barbie beds, shoes, lunchboxes, tents, chopsticks, corkscrews, and chainsaws, Mattel sought a new device to brand with the famous doll's image. In 2000, it settled on a PC, seen here, which ran Windows 98. Patriot, the company responsible for the Barbie PC, simultaneously released a Hot Wheelscomputer for boys. Like the toy, it was prone to frequent crashes. Samsung SPH-9000 (2006)In 2006, Samsung announced this tiny Windows XP device, which sported a 1GHz Transmeta CPU, a 5-inch LCD screen, a built-in camera, and Wi-Max support. It could fold in ways that would make a circus contortionist jealous. Accordingly, during its debut demonstration, Samsung representatives accidentally folded the SPH-9000 so many times that it disappeared in a reality-bending blink, stunning everyone in attendance. Jack PC (2010)I know what you're thinking: "I've always wanted a PC that fits in a tiny outlet box." (I also know what you're eating, but I won't mention it so I don't embarrass you.) Believe it or not, your wish was granted in the form of the Jack PC, a tiny thin-client computer unveiled in 2010 that did indeed fit in an outlet box. You stuck it in your wall and forgot about it—that is, until you tripped over the cords on your way back to the fridge. Maxdata Belinea s.book 1 Mini-Note (2008)At some point in the history of man (2008), someone had the idea to combine a netbook with a detachable Skype handset. The result was the "Maxdata Belinea s.book 1 Mini-Note," which sports a name that is at least twice as large as the computer itself. Precisely because of its strange features, people did not like the Maxdata Belinea s.book 1 Mini-Note, and it soon disappeared into the naked wilderness, never to be seen again. Sony VAIO VGX-TP25E (2008)In recent times, computers have shifted to the center of the modern media experience. That's a salesman's way of saying that you should buy a new home theater PC for $3,000—which is exactly what Sony hoped you'd do in 2008 when it released this giant hockey puck PC that could function as a DVR. Sony's HTPC also distinguished itself as the only PC that could easily roll down a hill. Critics weren't impressed, but the Association of Professional Computer Bowlers immediately fell in love. DreamCom Series 10 (2008)I know what you're thinking: "Didn't you already know what I was thinking earlier in this slideshow?" Yes, but you are also thinking that you'd love to have a laptop that could do whatever is happening in the photo above, albeit for under $2,000. Too bad! I have no evidence that the DreamCom 10 made it into production, but if it did, I'm sure it would have been $5,000 just to spite you. Space Cube (2006)Shimafuji Corporation developed the diminutive Space Cube PC for one purpose: space travel. Low-earth orbit is a place where the size and shape of this 52mm by 52mm by 55mm cube matter considerably because every ounce of payload dramatically raises the price of admission. It's unclear whether the Space Cube, which sports a 300MHz MIPS-based processor and 16 megs of RAM, has ever been sold to the public, but the tiny Japanese PC is available for extraterrestrial research, weddings, and bar mitzvah if desired. Lenovo ThinkPad W700DS (2008)With dual-screen desktop setups common these days, it was only a matter of time before someone created a dual-screen laptop. One such model by Lenovo, seen here, sports a clever second screen that slides out from behind the first, thus allowing you to easily regret the $5,000 you spent on it when it snaps off due to a clumsy patron at the coffee shop. (Razer teased something similar at CES 2017, so perhaps everything old is new again.) Commodore 64x (2011)Nope, this is not the vintage Commodore 64 (released in 1982) home computer you might be familiar with. In 2010, Commodore USA formed to revive the long-dead Commodore brand name. One of its first products, released in 2011, is the Commodore 64x, a modern x86 PC with an Intel Atom processor crammed into a new Commodore 64 look-alike case. Reportedly, the first run of 20,000 units sold out. Haier Heart v5 (2007)Working with a laptop computer can be very uncomfortable for extended periods of time—especially if you place it on your lap. To partially remedy this problem, Chinese PC manufacturer Haier released this strange notebook with an extending, very-adjustable display in 2007. Of all the bizarre PC designs on this list, this one looks like it might be the most useful. It also looks most likely to suddenly remove your digits by accident. But hey, that's just part of being bizarre.
|
Archives
November 2023
|
|
2951 Britannia crescent
Port Coquitlam BC, V3B 4V5 778-776-6222 Hours of operation Mon - Fri 9 a.m. - 6 p.m. Sat 11 a.m. - 5 p.m. (by appointment only) Sunday & Holidays - Closed |
Business Number 778569517BC0001 - © Copyright CompuBC, All Rights Reserved.
|